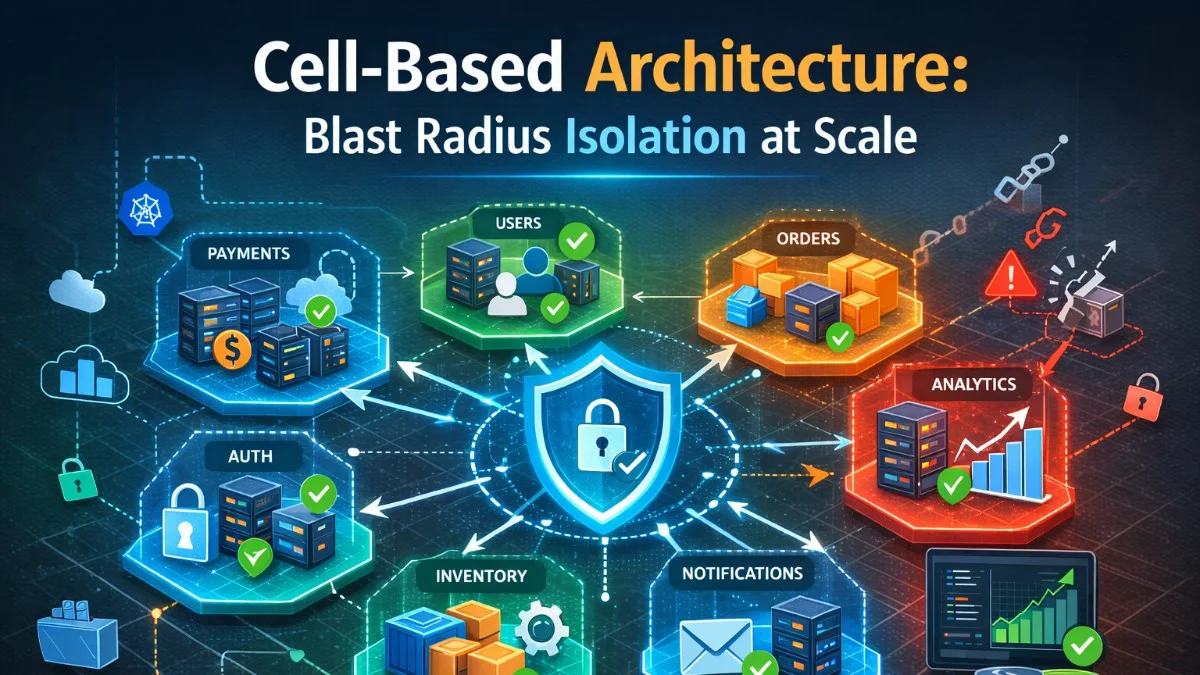
Cell-Based Architecture: Blast Radius Isolation at Scale
When a single availability zone or region isn't enough isolation, cell-based architecture lets you contain failures to a fraction of your users. Here's how it works and when to use it.
System design, patterns, and architectural decisions.
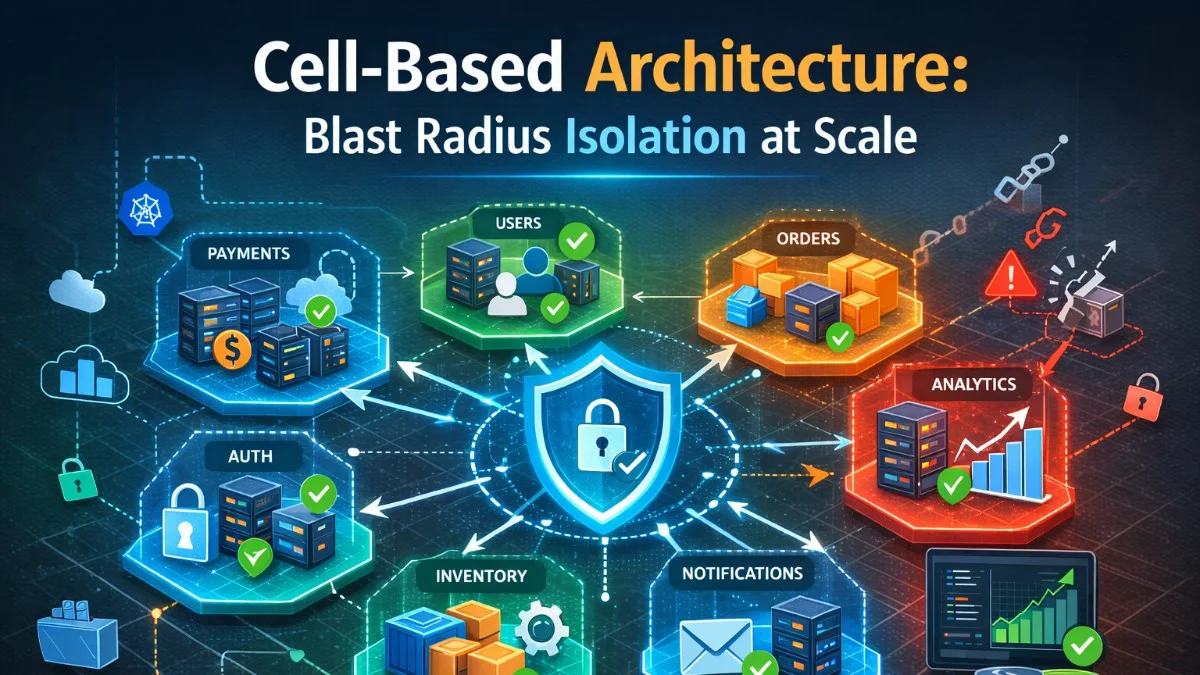
When a single availability zone or region isn't enough isolation, cell-based architecture lets you contain failures to a fraction of your users. Here's how it works and when to use it.
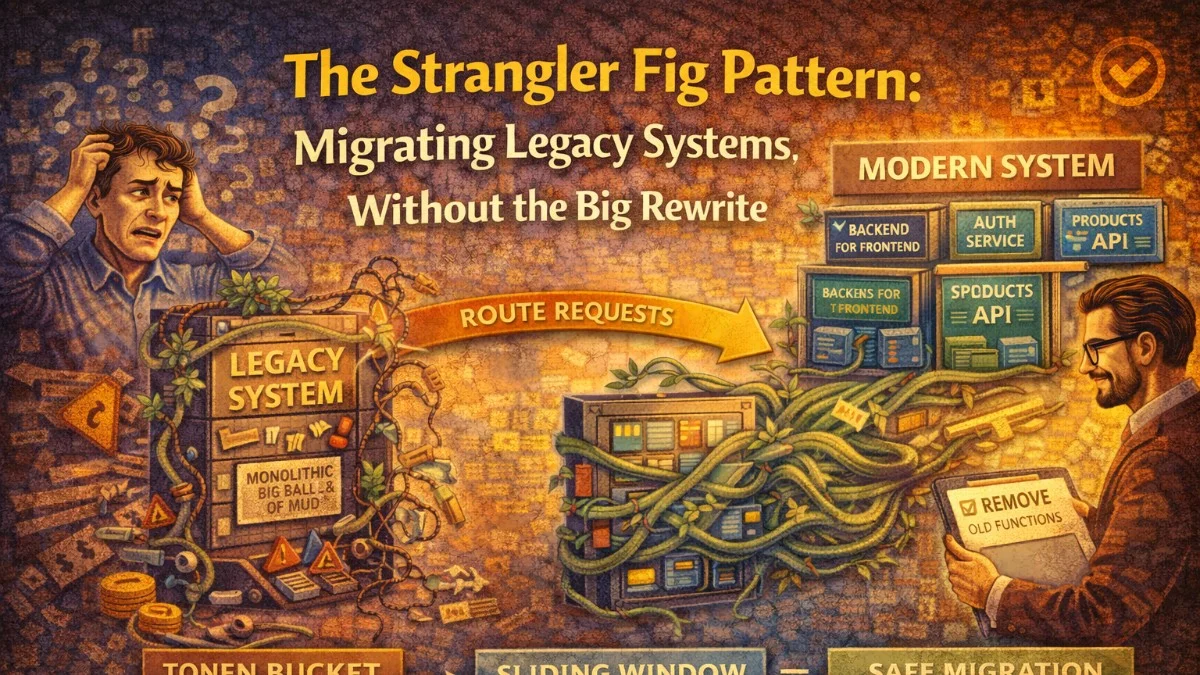
Big-bang rewrites fail more often than they succeed. The strangler fig pattern lets you replace a legacy system incrementally, keeping the lights on while modernizing underneath it.
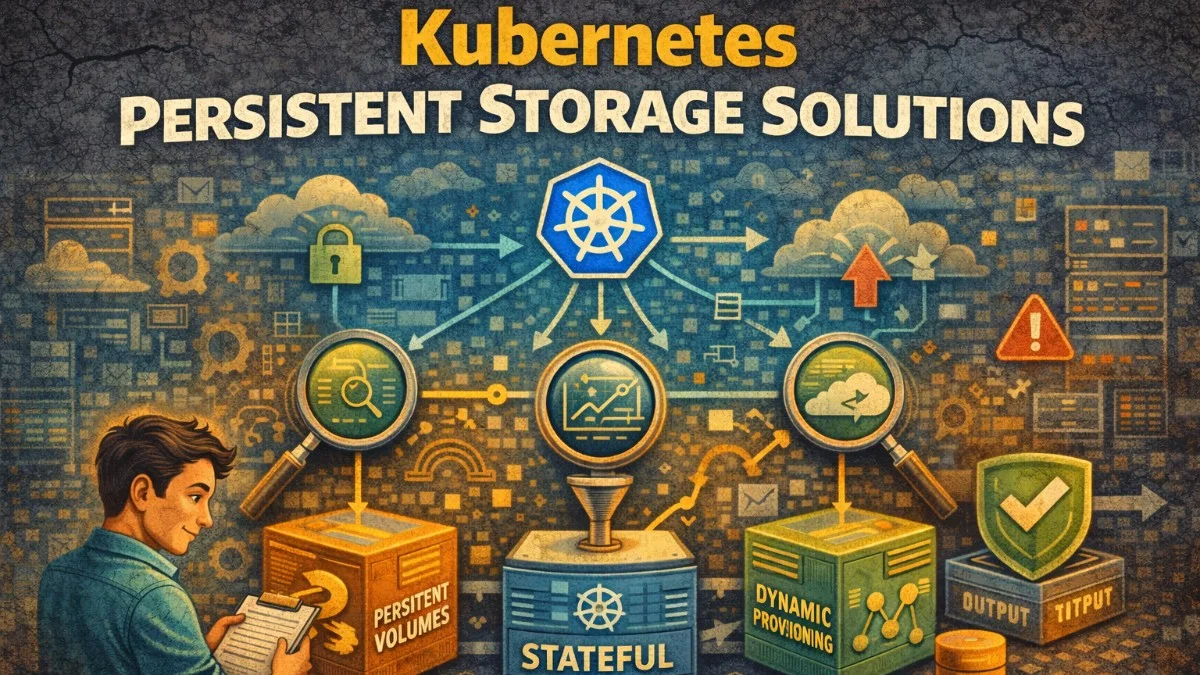
Manage stateful workloads in Kubernetes. Compare storage classes, CSI drivers, and backup strategies.
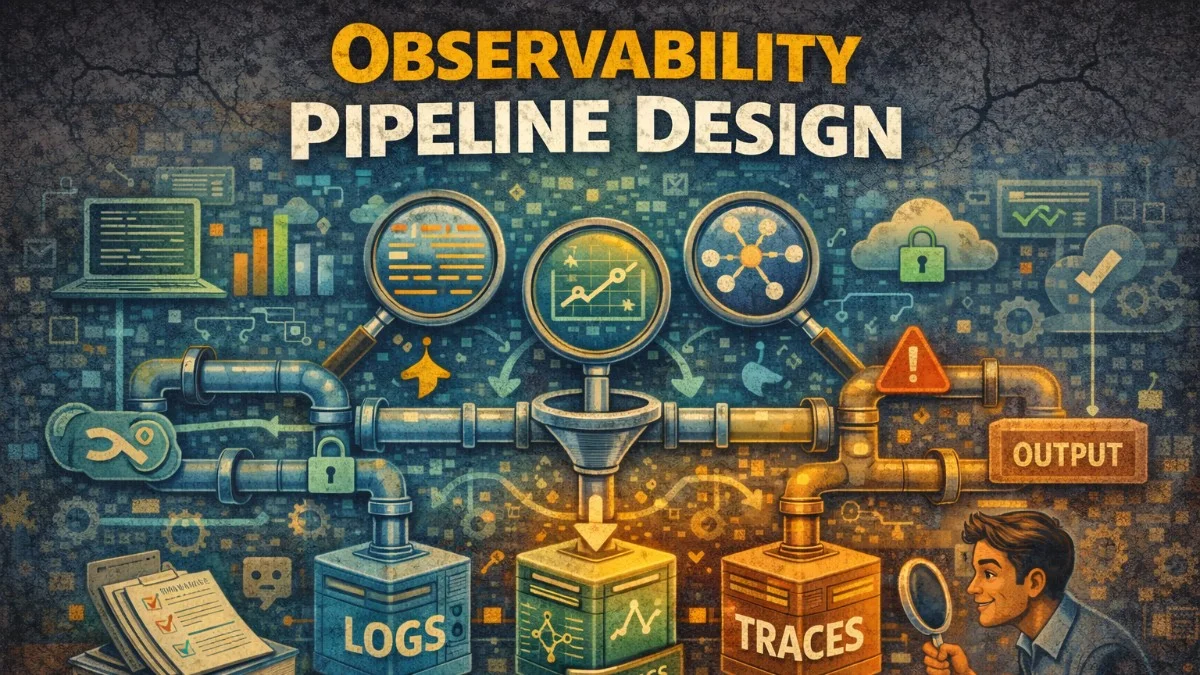
Build scalable observability infrastructure. Collect, process, and store telemetry data efficiently.
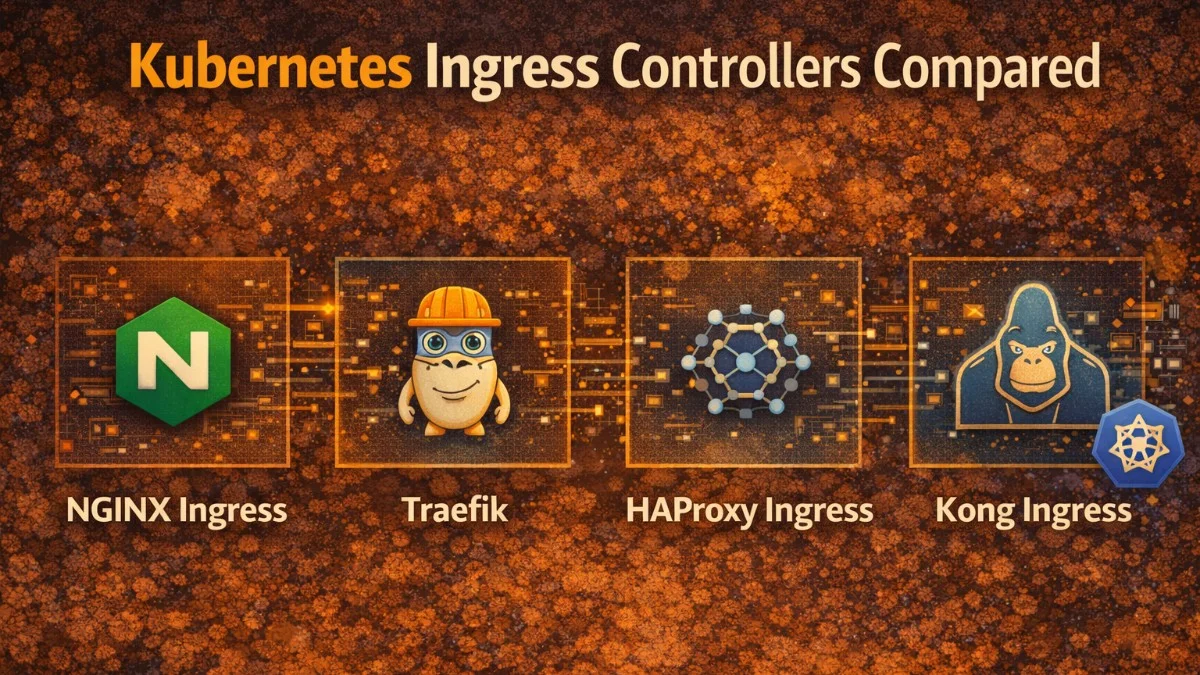
Choose the right ingress controller. Compare NGINX, Traefik, HAProxy, and cloud-native options.
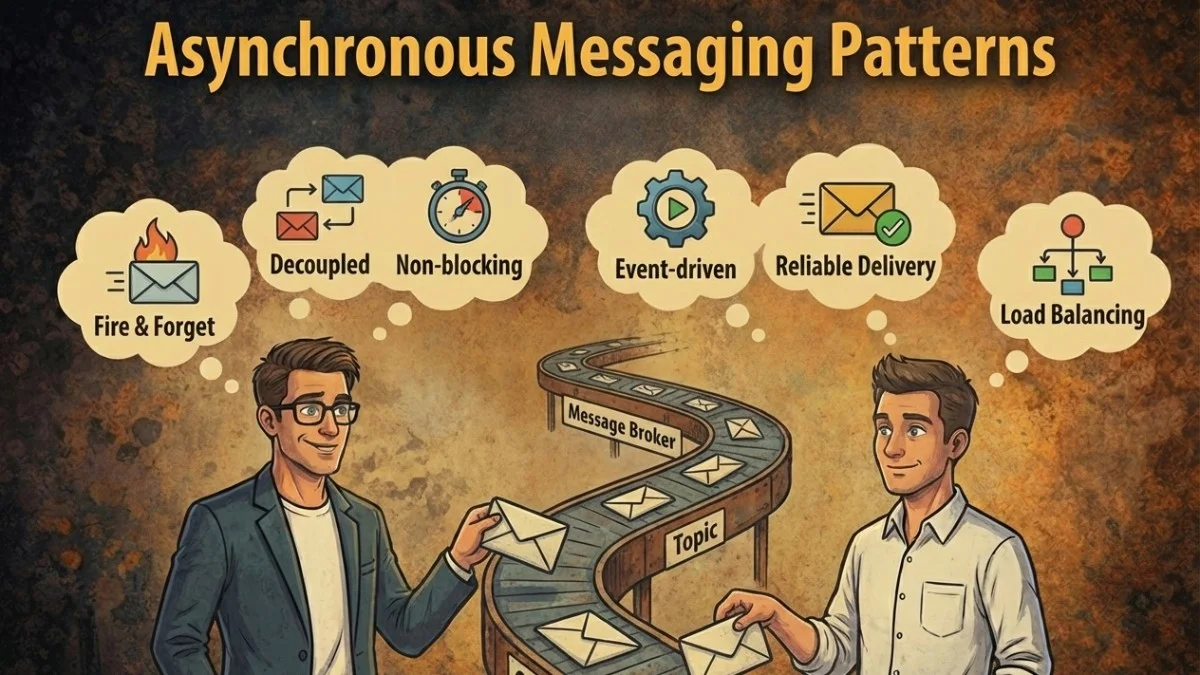
Design reliable async communication. Learn competing consumers, saga pattern, and transactional outbox.
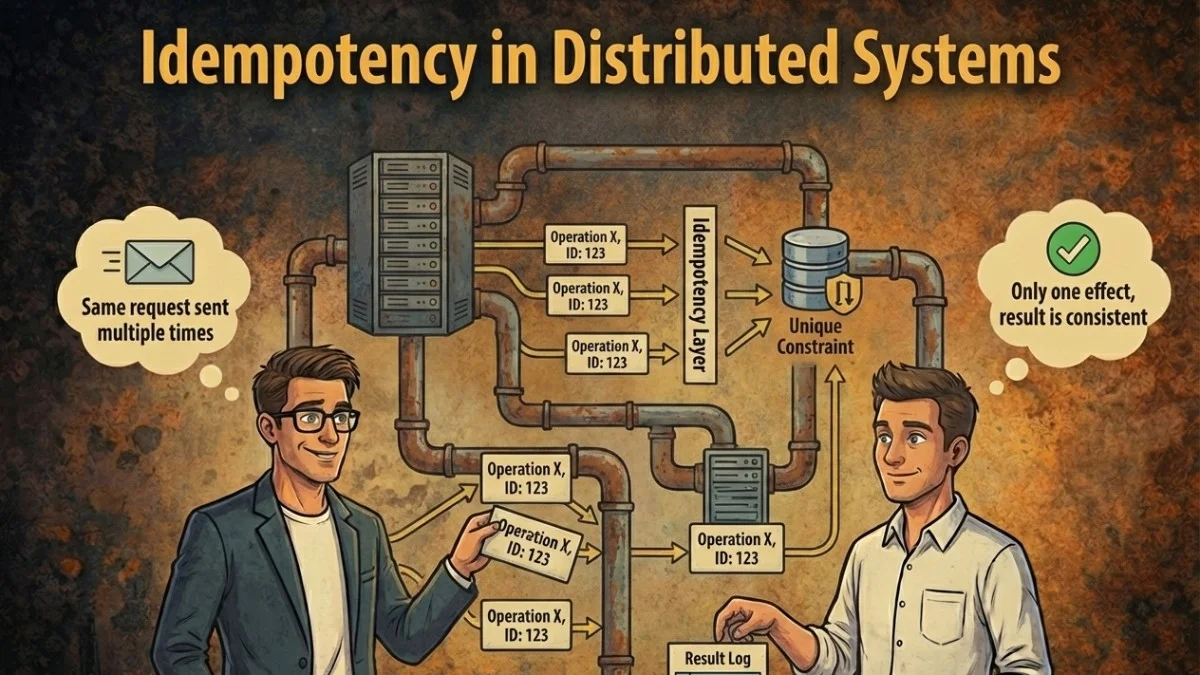
Design idempotent APIs and operations. Handle retries safely with idempotency keys and deduplication strategies.

Implement service mesh for microservices. Learn Istio and Linkerd patterns for traffic management and observability.
Choose the right serialization format. Compare JSON, Protocol Buffers, Avro, and MessagePack for different use cases.

Build systems that handle failure gracefully. Implement bulkheads, timeouts, retries, and fallback strategies.
Understand how containers communicate. Learn bridge networks, overlay networks, and CNI plugin architecture.
Centralize logs from distributed systems. Build searchable, structured logging with correlation and alerting.
Let's discuss how we can help you build reliable software.
We use cookies to analyze site usage and improve your experience. By continuing to use this site, you agree to our use of cookies. Learn more about our privacy policy