
Why Milestone-Based Delivery Beats Hourly Billing
Hourly billing creates misaligned incentives. Here's why milestones work better for everyone.
Insights on software development, technical strategy, and building reliable systems.

Hourly billing creates misaligned incentives. Here's why milestones work better for everyone.
The statistic is sobering: 70% of software projects fail to deliver on time, on budget, or on scope. Here's what causes these failures and how to prevent them.

Technical debt is inevitable, but it doesn't have to be unmanageable. Learn strategies for keeping it under control.
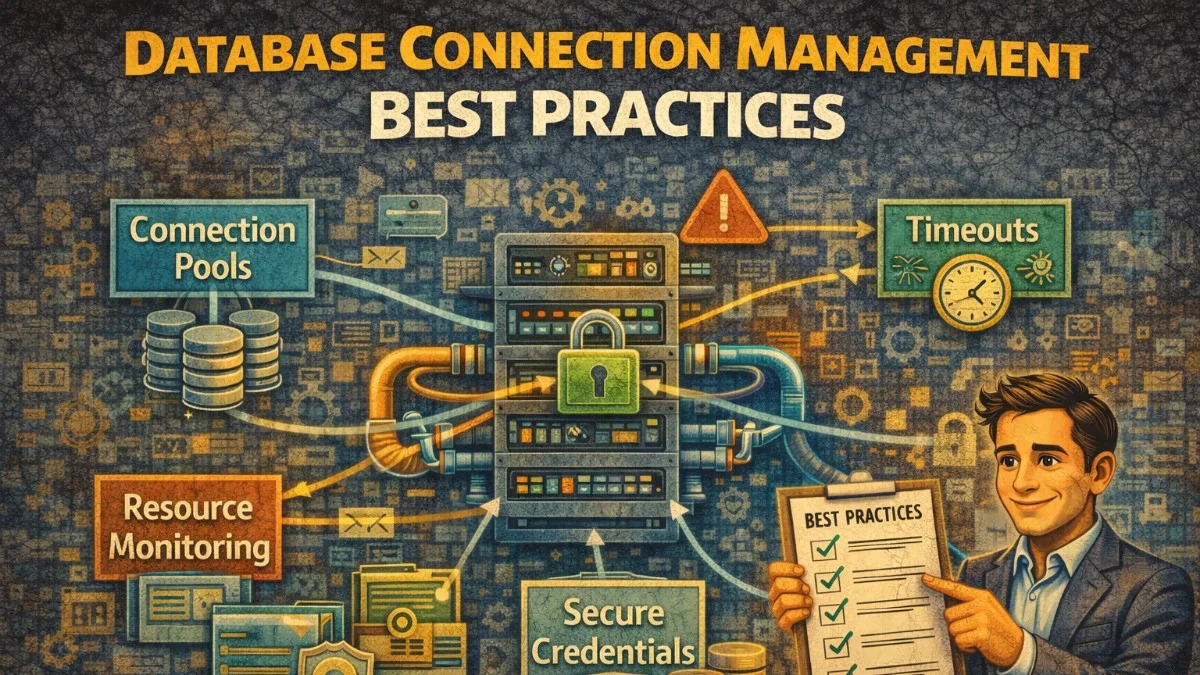
Manage database connections efficiently. Handle connection limits, timeouts, and connection lifecycle properly.

Most agencies track too many metrics and miss the ones that actually predict profit. Here's what to focus on.
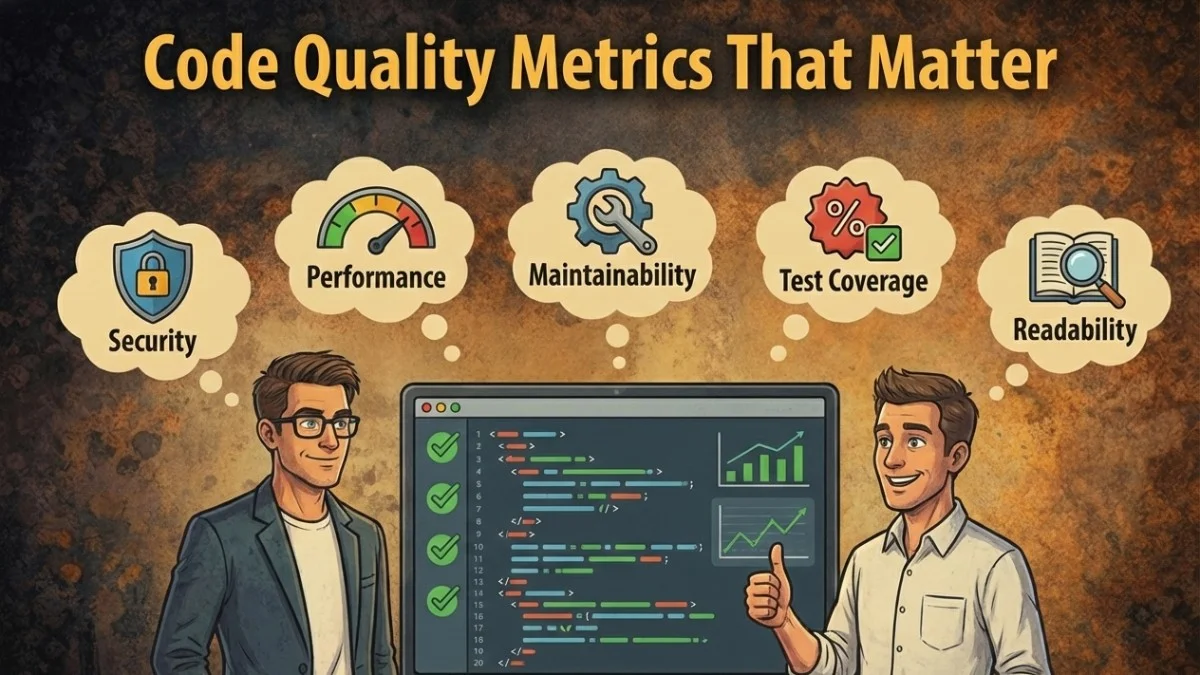
Measure code quality effectively. Track meaningful metrics, avoid vanity metrics, and improve team practices.

Your clients want to know what's happening. They just don't want to bother you to find out.
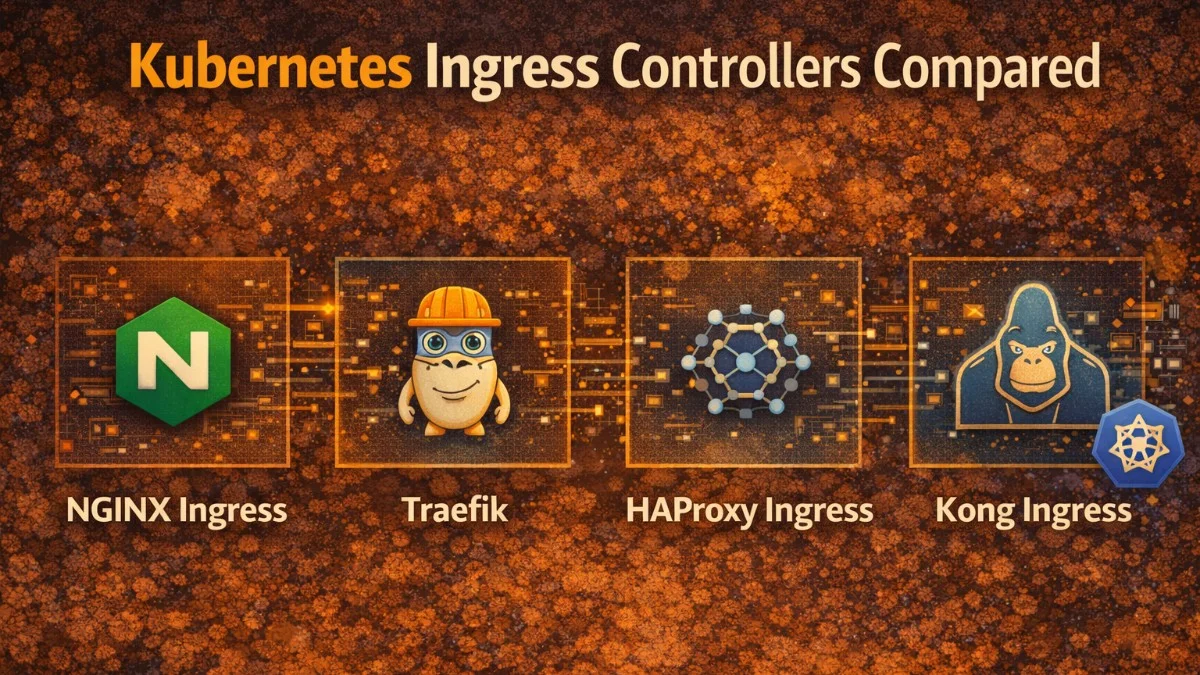
Choose the right ingress controller. Compare NGINX, Traefik, HAProxy, and cloud-native options.

Counterintuitive insight: the most detailed scope documents often have the most scope creep.
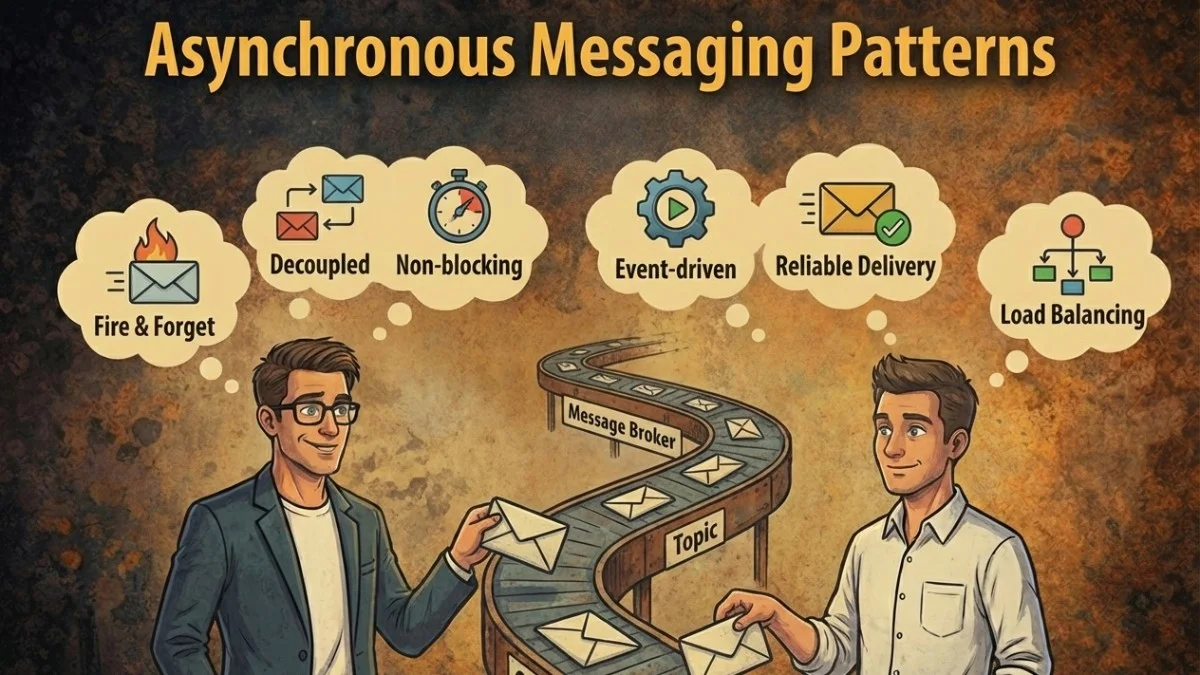
Design reliable async communication. Learn competing consumers, saga pattern, and transactional outbox.
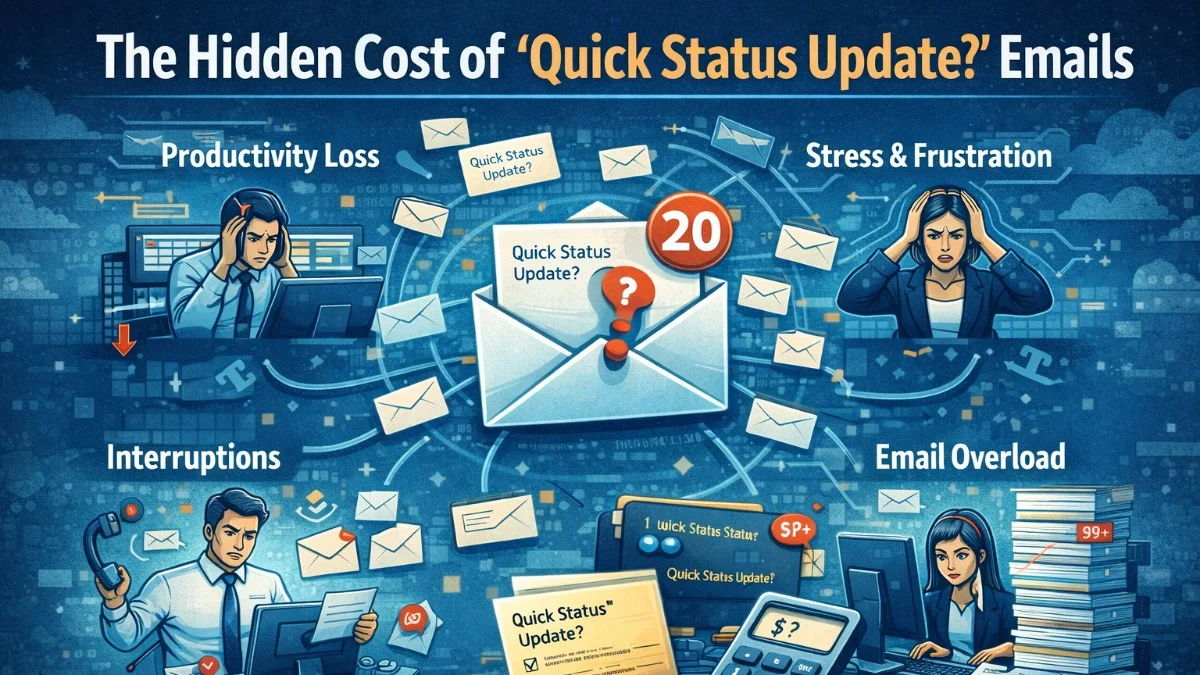
Every "where are we on this?" email costs more than you think. Here's what we've learned about proactive client communication.
Master Prometheus for application monitoring. Learn PromQL, alerting rules, and Grafana dashboard best practices.

We analyzed 150 agency projects. The margin leakage was worse than expected.
Protect your data with robust backup strategies. Implement point-in-time recovery, automated backups, and disaster recovery.

Your clients aren't reading your detailed scope documents. Here's what actually works.
Let's discuss how we can help you build reliable software.
We use cookies to analyze site usage and improve your experience. By continuing to use this site, you agree to our use of cookies. Learn more about our privacy policy